Cybercrime was as obscure a topic to write about a generation ago as quantum physics or changes in the derivatives market. It now serves as a major plot point in numerous novels. We are constantly being attacked, whether it’s by criminal gangs using phishing to steal private information to sell on the dark web, by that guy from college catfishing people on Facebook, or by the daily SMS urging us to click a link to claim a reward. Everywhere we look, someone is attempting to use the technology on which we rely, against us, like pension scams, identity theft, strangers stalking our kids on TikTok, etc. Here are 10 best books based on cybercrime.
10 Best Books Based On Cybercrime
The Witness By Nora Roberts
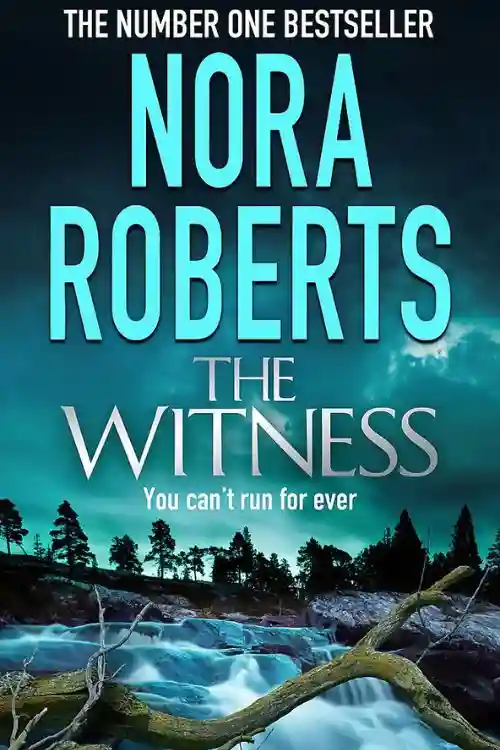
Elizabeth, the daughter of a strict mother, was finally able to let loose one night when she went out drinking and let a strange man with a seductive Russian accent draw her to his home on Lake Shore Drive. Her life was profoundly altered by what transpired next. Twelve years later, Abigail Lowery is a lady who resides on the outskirts of an Ozarks tiny town. She works as a freelance programmer and creates complex security systems. She also has a powerful dog and a variety of weapons for further protection. She doesn’t talk much and doesn’t share much.
Police chief Brooks Gleason, though, is merely intrigued by Abigail’s reserve. He is fascinated by her, yet frustrated by her unromantic perspectives, rational thinking, and private personality. He has a suspicion Abigail needs to be protected from something, and that her strong barriers conceal a tale that has to be told. Nora Roberts introduces a gripping new novel with a quirky, lovable heroine and a heart-pounding plot that solidifies her position as today’s most consistently entertaining Thriller author and will leave readers craving more.
Ghost In The Wires By Kevin D. Mitnick
The most evasive hacker to ever access a computer was Kevin Mitnick. No matter how fast the authorities were, Mitnick was faster, dashing across phone switches, computer systems, and cellphone networks to access computers and networks at the biggest companies in the world. In an increasingly complex game of hide and seek that involved phony identities, numerous places, and numerous close calls, Mitnick fled as the FBI’s net finally started to close in, eventually coming face-to-face with the feds who would stop at nothing to bring him down.
Ghost in the Wires is a gripping true account of Mystery, suspense, and incredible escapes that paints a picture of a visionary who compelled authorities to re evaluate their pursuit of him and compelled businesses to reconsider how they safeguard their most confidential data. If there were a hall of fame or shame for computer hackers, a plaque honouring Kevin Mitnick would be placed close to the front door. This skilled break-artist was accessing the digital secrets of Sun Micro systems, Digital Equipment Corporation, Nokia, Motorola, Pacific Bell, and other enormous corporations while other nerds were fumbling with possible passwords. In his autobiography Ghost in the Wires, he portrays himself as a tenacious recluse who is driven by a love of cunning rather than money gain.
Future Crimes By Marc Goodman
The world has profited greatly from technological advancements, but there is a sobering downside: our technology can be used against us. Hackers are using social media posts to plan home invasions, burglars are using baby monitors to snoop on families, and stalkers are using GPS on smartphones to follow their prey everywhere they go. All of us are aware that modern thieves are capable of stealing identities, depleting online bank accounts, and destroying computer servers, but that is only the beginning.
A frightening fact considering our extreme reliance on computers for everything from our country’s electrical system to air traffic control to financial services is that no computer has ever been made that cannot be compromised. Marc Goodman takes readers on a fascinating trip through the most sinister corners of the Internet with stunning insights based on a career in law enforcement and counter terrorism. Future Crimes examines how criminals are poised to take use of emerging technologies, such as robots, synthetic biology, nanotechnology, virtual reality, and artificial intelligence.
The book reads like science fiction yet is grounded in scientific truth. These fields have the potential to usher in a period of unheard-of affluence and abundance. But the technological foundation on which we are constructing our shared future is incredibly unstable and, like a house of cards, is liable to collapse at any time. A startling look at the shadowy side of technological advancement and the unexpected implications of our connected society may be found in Future Crimes. Goodman provides a clear path for us to follow in order to survive the advancement that is taking place in front of us. Future Crimes will serve as an urgent call to action that demonstrates how we may regain control over our own gadgets and utilise technology’s immense power for the sake of humanity before it’s too late. It is provocative, thrilling, and ultimately liberating.
Countdown To Zero Day By Kim Zetter
A apparently unrelated occurrence happened five months later. A computer security company in Belarus was contacted to debug certain Iranian machines that were stuck in a reboot loop, continuously crashing and rebooting. The company’s technicians initially thought the malicious code they discovered on the machines was a straightforward, commonplace piece of malware. But as they and other scientists from around the world looked into it, they found a virus with unmatched intricacy and a mystery origin and purpose.
They soon discovered that they had stumbled onto the first digital weapon in history. As it became known, tuxnet was unlike any virus or worm ever created before: It was the first attack to physically damage the machinery those computers were designed to operate in addition to the computers themselves. It was a clever strike, jointly prepared by the US and Israel, that went off without a hitch—until the restarting computers revealed everything. And Stuxnet’s discovery was only the beginning: When the digital weapon was discovered and broken down, it revealed hints about other tools that were out in the world. Security specialists soon discovered and exposed not one, but three extremely sophisticated digital spy tools that originated from the Stuxnet-creating laboratories.
Kim Zetter, a senior correspondent at Wired, has been one of the best writers in the world on the topic of hackers and computer security since 1999. After Stuxnet was discovered, she was one of the first writers to cover it, and she has written many of the most in-depth stories about it. In COUNTDOWN TO ZERO DAY: Stuxnet and the Launch of the World’s First Digital Weapon, Zetter elaborates on this work to demonstrate how the code was created and released as well as how its use opened a Pandora’s Box and ushered in an era of digital warfare in which any nation’s infrastructure—power grids, nuclear plants, oil pipelines, and dams—is susceptible to the same kind of attack with potentially disastrous results.
Digital Fortress By Dan Brown
Dan Brown’s riveting book, Digital Fortress, focused his razor-sharp research and storytelling abilities on the National Security Agency, the world’s most potent intelligence agency, before the multi-million dollar, blockbuster bestseller The Da Vinci Code. The National Security Agency contacts its head cryptographer, Susan Fletcher, a clever and attractive mathematician, when it runs into a peculiar code that it cannot decipher. The power corridors are shocked by what she discovers.
Instead of weapons or bombs, the NSA is being held captive by a code so intricate that its disclosure will seriously impair American intelligence. Fletcher fights to save the organization she believes in while caught in an escalating tidal wave of secrecy and deception. She finds herself fighting not just for herself after being betrayed by everyone. A former NSA employee is holding the surveillance data of a country hostage in the techno-thriller book Digital Fortress and the efforts made by the government to recover this important knowledge.
Ensei Tankado, a former NSA employee, is uneasy about the government’s national surveillance tactics. In order to effectively contain the knowledge, he therefore develops a sophisticated new code, essentially holding the NSA hostage. When Ensei passes away from a heart attack, things get more difficult for the NSA’s chief cryptographer, who is tasked with cracking the code for the so-called “digital fortress”. Anyone who is able to get their hands on the code can take it. As the government, mystery assassins, and an unidentified vested party race against time,
Sandworm By Andy Greenberg
The world saw the beginning of a mystery wave of cyberattacks in 2014. The attacks grew bolder and bolder, focusing on American utility firms, NATO, and Eastern European electric systems. They came to a head in the summer of 2017, when the NotPetya malware was released, infiltrating, upsetting, and crippling some of the biggest companies in the world, from pharmaceutical companies to software makers to shipping firms. ATMs froze at the attack’s focal point in Ukraine. The mail and railroad networks were shut down. Hospitals lost power.
The largest and most damaging cyberattack the world had ever seen, Not Petya spread over the globe and caused damage of an incredible 10 billion dollars. The group of hackers known as Sandworm, who are behind these attacks, are swiftly establishing themselves as the most dangerous cyberwarriors in history. They are a relentless, highly talented group working for Russia’s military intelligence agency, and their desire to unleash broad, uncontrolled attacks on their enemies’ most vital infrastructure matches their skills.
They both target the military and citizens, as well as the public and private sectors. Sandworm examines the threat that this force poses to our stability and national security in a tense, global detective thriller. Sandworm shows the facts of not just Russia’s global digital attack but also of a time when conflict is no longer fought on the battlefield as the Kremlin’s role in foreign government manipulation comes into sharper focus. It demonstrates how the distinctions between virtual and actual warfare, as well as between war and peace, have started to wane, with potentially catastrophic results.
Zenobia July By Lisa Bunker
It’s a new chapter in Zenobia July’s life. She now resides in Maine with her aunts after formerly living in Arizona with her father. She used to spend the most of her time working on her excellent coding and hacking talents in front of a computer screen, but now days she is breaking out of her shell and finding a community of friends at Monarch Middle School. She used to be told she was a guy, but now she can live openly as the girl she has always been. While coping with the difficulties of a new school, a new family, and coming to terms with revealing her true gender for the first time, Zenobia feels she is the one with the skills to solve the riddle when someone anonymously puts terrible memes on her school’s website. Zenobia July is a timely and moving novel that is fundamentally a tale about coming home.
American Kingpin By Nick Bilton
The Silk Road, a secret Web site hosted on the Dark Web where anybody may trade anything—drugs, hacking software, false passports, counterfeit money, poisons—free from the government’s watchful eye, was established in 2011 by 26-year-old libertarian programmer Ross Ulbricht. It didn’t take long for the media to learn about the new website where anyone could buy and sell contraband without being detected, including terrorists and black hat hackers in addition to kids and marijuana sellers. An epic two-year manhunt for the site’s elusive owner was begun by the federal government after a public outcry, but there were no leads, no witnesses, and no established jurisdictions.
The only thing the detectives were certain of was that the site’s administrator went by the name of the Dread Pirate Roberts. As The Silk Road swiftly grew to become a $1.2 billion business, Ross accepted his new position as kingpin. He assembled a devoted band of supporters in both high and low places, all of whom were as fixated on the excitement and danger of operating an illicit market as his clients were on the heroin they sold. He learned about the target on his back through his network and immediately took severe measures to defend himself, including arranging a hit on a former employee. The Federal Government raced against time to apprehend Ross as he made plans to vanish forever while trying to find him in the global Internet’s “haystack” of information.
Kingpin By Kevin Poulsen
The real-life account of Max Butler, a brilliant hacker was the head of a billion-dollar cybercrime organization. The rumour that a bold criminal had undertaken a hostile takeover of an online criminal network that had stolen billions of dollars from the US economy quickly went across the hacking underground. The perpetrator was a great coder with a hippie philosophy and a secret identity as a supervillain. White-hat hacker Max “Vision” Butler was well-known in the programming community and even worked as a consultant for the FBI. But Max had a second personality.
He had observed the scammers around him as the black-hat “Iceman argue, their ranks beset by infiltrators, and their techniques ineffective. KINGPIN exposes the workings of a silent crime wave that affects millions of people globally through the tale of Max Butler’s amazing ascent to prominence. It reveals enormous online-fraud marketplaces packed with credit card information, forgeries, compromised bank accounts, and bogus passports. We get an inside look at the quiet, desperate battle that law enforcement wages against these con artists through to Kevin Poulsen’s unparalleled access to both police and criminals discover that the boy next door might not be who he appears to be.
Spam Nation By Brian Krebs
Investigative reporter and cybersecurity specialist Brian Krebs exposes the criminal masterminds behind some of the largest spam and hacker operations that target Americans and their bank accounts in his book, Spam Nation. He provides the first comprehensive account of the global spam issue and the damage it poses to customers everywhere by tracing the emergence, collapse, and terrifying resurgence of the digital mafia that was responsible for the two largest spam pharmacies and numerous malware, phishing, and spyware campaigns.
This horrifying real story explains how we inadvertently allow these digital thieves into our lives every day through cutting-edge research, investigative reporting, and first-person interviews. Krebs reveals the shocking lengths to which these individuals will go in order to profit from our data and our wallets, from the unassuming computer programmers right next door to the cybercriminals like “Cosma” who launched a massive malware attack and stole the logins and passwords of thousands of Americans.
Even people who never read spam mails are at risk because hundreds of thousands of Americans are exposing themselves to fraud and poisonous products from shady online pharmacies. Krebs points out that spammers are able to access accounts through these emails, steal user names and passwords, and then resell them on the online black market. The consequences of this global epidemic cost consumers and businesses billions of dollars, but they also kill lives. In the end, Spam Nation makes specific recommendations for how to safeguard our online safety and stop this tsunami of cybercrime before it’s too late.
Also Read: 10 Best Villains Ever Cast by Marvel for Movies